Table of Content
Why Manual Defence is no longer fit for Purpose
In the time it takes to conduct a standard morning stand-up or grab a coffee between meetings, a modern adversary has likely already breached your perimeter and begun moving laterally through your sensitive data.
As a security consultant, I often see organisations still relying on traditional, manual workflows for alert triage. But the latest industry data suggests that the window for human intervention has effectively slammed shut. According to the 2025 Global Threat Report, average adversary "breakout times" - the interval between initial access and lateral movement - have plummeted to just 48 minutes. Even more sobering is the fact that the fastest recorded breakout occurred in a staggering 51 seconds.
If your Security Operations Centre (SOC) is still operating on a "minutes-to-hours" ticket lifecycle, you aren't just behind the curve; you’re effectively out of the race.
The Rise of the "Ghost" Intrusion
The challenge isn't just speed; it’s visibility. We are firmly in the era of the "malware-free" attack. Recent findings show that 81% of hands-on-keyboard intrusions are now malware-free. Adversaries are no longer dropping noisy, recognisable files that trigger traditional antivirus software. Instead, they are "living off the land" - using legitimate credentials and native administrative tools to blend in with your everyday traffic.
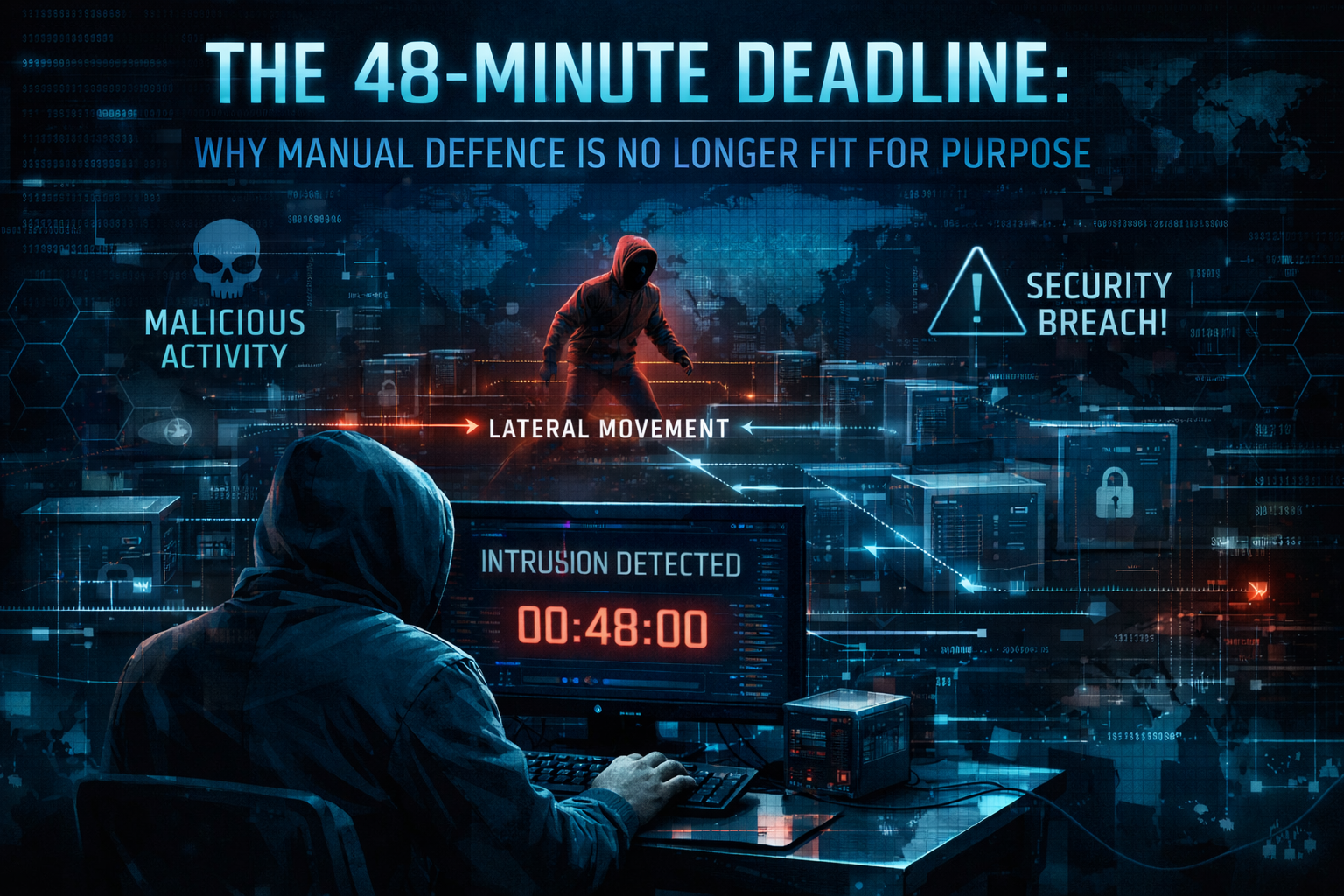
When an attacker isn't using malware, there is no "signature" to find. Manual detection in this environment requires an analyst to distinguish between a legitimate admin doing their job and a threat actor using those same tools to exfiltrate data. By the time a human identifies the anomaly, the 48-minute window has usually expired.
Why Manual Response is the New Bottleneck
In a manual SOC, the process is familiar: an alert is generated, triaged, a ticket is raised, and eventually, a human investigates. In a world of 48-minute breakouts, this process is a structural vulnerability.
Manual response cannot scale to meet the "industrialised" nature of modern cybercrime. When adversaries leverage AI to automate their reconnaissance and vulnerability scanning, they operate at a tempo that human-centric teams simply cannot match.
Operating at an "EPIC" Tempo
At Cyber Context, we believe that defending the modern enterprise requires a fundamental shift in philosophy. We advocate for a Threat Informed, AI-Driven Defence that prioritises what we call an "EPIC" outcome: Excellence, Pace, Integrity, and Care.
In this context, Pace is the most critical variable. To neutralise a threat that moves in 48 minutes, your detection systems must operate in seconds. We leverage AI-native platforms that don’t just wait for a file to be dropped; they monitor behavioural patterns across the entire digital estate.
By using AI to correlate billions of signals in real time, we can identify subtle signs of lateral movement - such as credential abuse or unusual service account activity - within seconds of a suspected threat. This enables autonomous response actions, such as suspending compromised accounts or initiating password resets, before the adversary can achieve their objective.
The Bottom Line
The 48-minute breakout time is a clear signal from the threat landscape: the "wait and see" approach to security is dead.
To safeguard your organisation in 2026, your defence must be as nimble and dynamic as the adversaries you face. It’s time to move beyond manual bottlenecks and embrace a security posture that operates at machine speed.
Is your organisation ready to break the 48-minute barrier? Let’s discuss how we can accelerate your defence.
.png)
Stay Ahead in Cloud Security
Get the latest insights and updates on cloud security.
Trusted by industry leaders worldwide
.png)
.png)
.png)
.png)
.png)